Nowadays, it is undeniable to state that business and organizations (be they private companies or public institutions) are supported by information technology. We are in fact in the era of information technology. Information technology or IT uses computers and storage networking to construct, hold, develop and safeguard electronic data.
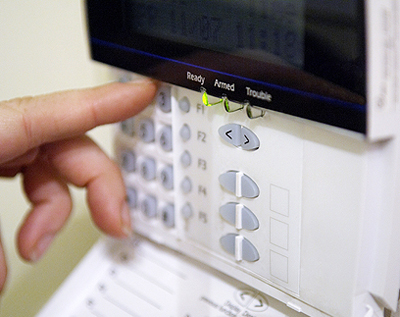
It is crucial for businesses to keep information safe, or else have the company at risk; vulnerabilities can directly impact a business’s day-to-day operations. One way of deterring the theft of internal information is to heighten business security from all technological standpoints. And it should be done as soon as possible.

In this sense, addressing business security means the implementation of security mechanisms and tools that are based on the following principles:
- The principle of confidentiality, which is characterized by the protection of information against unauthorized access.
- The principle of availability, which is established as the prevention of interruptions in the operation of systems and access to information when necessary.
- The principle of integrity, which translates into protection against tampering and improper changes.
- The principle of authenticity, which reflects the identification of anyone who has access to the information or who performs any operation that uses it.
- The principle of legality, which is conceptualized as the protection of information—in the sense of guaranteeing its preservation (in accordance with legal precepts).
- The principle of auditability, which means the configuration of systems and databases in order to enable the tracking of physical and logical activities.
In order to understand the scope of information security, it is necessary to observe the main aspects of this scenario:
- Physical – facilities, equipment, infrastructure, and inputs
- Logical – information, systems, storage, system and database construction
- Environmental – IT, locations, lay-outs, connections, segregation of environments
- Organizational – activities, people, segregation of functions, knowledge, awareness, commitment
- Communication – Internet, intranet, e-business, e-mail